Can you imagine living on 100% renewable energy? This poses formidable challenges to electrical grids in terms of quality of service and energy balance. Our goal is to propose solutions to these challenges, by inventing innovative methods that combine information and communication technology with new electrical devices that can store energy. To reach this goal, we explore 4 complementary directions: monitoring, control, electric devices, and cyber-security.
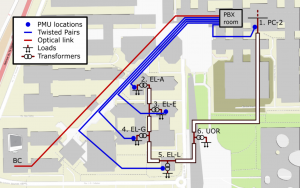
We are building an innovative monitoring infrastructure on the EPFL campus grid. EPFL is the first in the world to deploy such a system. It comprises a reliable, autonomous communication network and tailor-made real-time control software. Today, six buildings are monitored by a state estimation process that is fed by 5 phasor measurement units (PMUs). We also keep an open record of all past measurements, for research purposes.
We are developing a framework, called “Commelec”, to control an electrical grid in real time, even if the grid has very little inertia, as is typical when there is a large amount of distributed generation. Its solves the problems of quality of service and energy balance without major investment. The framework provides a “Grid Operating System” that allows device controllers for intelligent buildings, e-car charging systems, etc. to be easily connected and provide real time support to the grid. More information…

Smart grid being a critical infrastructure, cyber-security is identified as one of the key components to guarantee its reliable operation. Hence we are developing a comprehensive security framework for our campus smart grid to protect it from cyber attacks. Our security mechanisms comprise of authenticated and accountable access to devices and services in the grid, end-to-end secure data communication among devices and ensuring a secure perimeter by means of firewalls and a proxy server at the DMZ (Demilitarized Zone) that censors any communication between the smart grid and the outside world.
